WordPress powers over 40% of websites, making the login page a frequent target for cyberattacks, especially brute-force attempts and bot traffic. Traditional methods—strong passwords and two-factor authentication—are helpful, but adding Cloudflare Zero Trust offers a far more robust, identity-aware access control that shields wp-login.php before threats hit your server.
Cloudflare Zero Trust blocks brute-force attacks on wp-login.php by putting a security gate in front of your login page, requiring user authentication before the actual login screen loads.
Prerequisites
- Your WordPress site must be live and use Cloudflare DNS with proxy enabled.
- You need a Cloudflare Zero Trust account (the free tier allows up to 50 users).
- It’s best to have a list of email addresses approved to access WordPress, or decide on authentication methods (OTP, Google, etc.).
Step-by-Step Integration Guide
1. Create Cloudflare Zero Trust Account
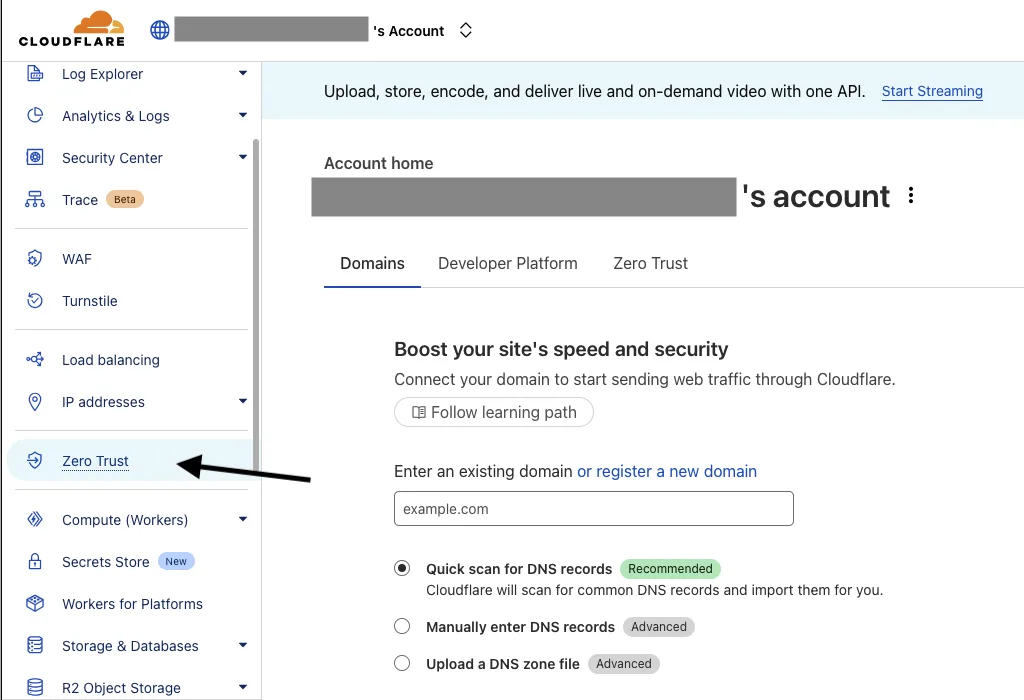
- Log in to your Cloudflare account and sign up for a Zero Trust account.
- Follow the initial setup guidance provided by Cloudflare.
2. Access Cloudflare Zero Trust Dashboard
- Log into Cloudflare, navigate to the Zero Trust dashboard.
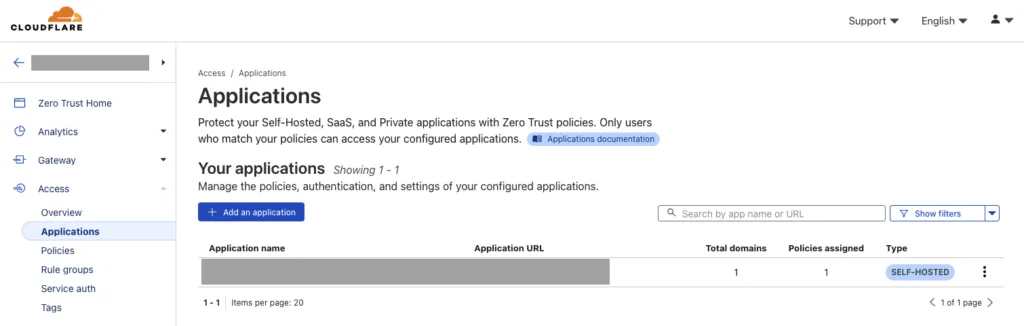
- Under “Access”, click on “Applications”.
- Click “Add an application” and choose “Self-hosted” since WordPress is self-hosted.
3. Configure Application Protection
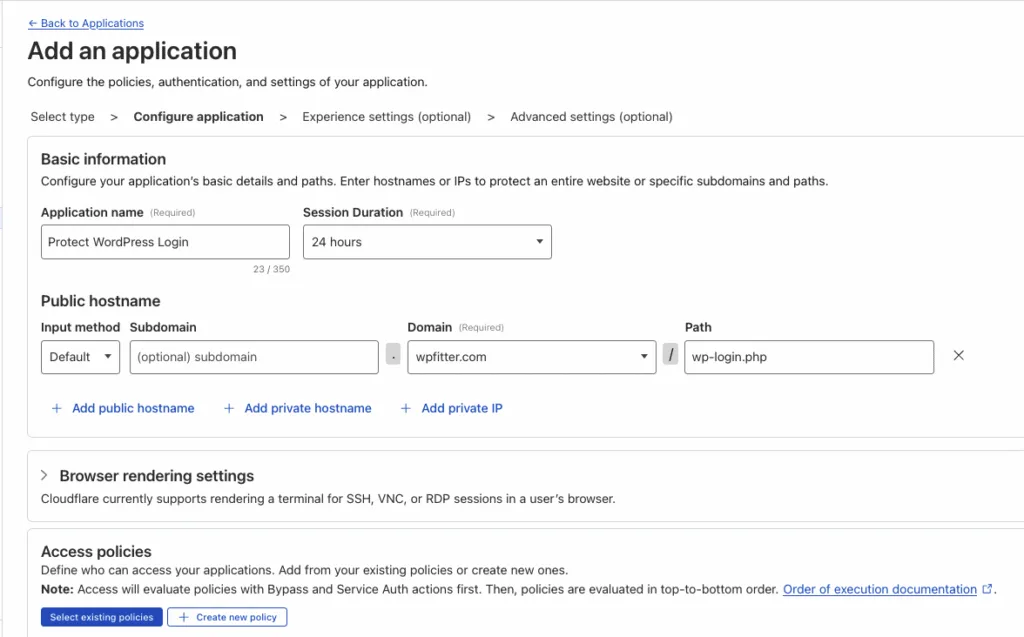
- Name your application (e.g. “WordPress Login”).
- Set your domain (and subdomain if needed).
- Set what you want to protect: use
/wp-login.php.
Decide who can access:
- Create an Access Policy for approved emails.
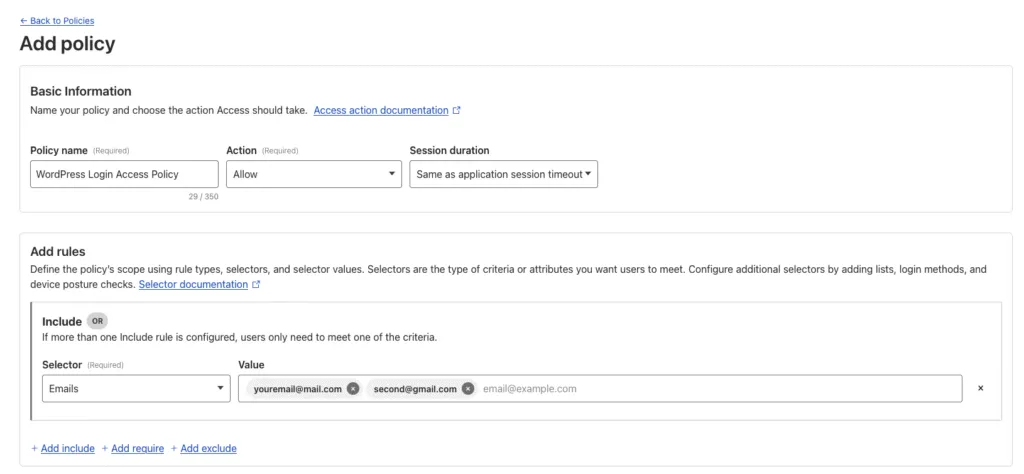
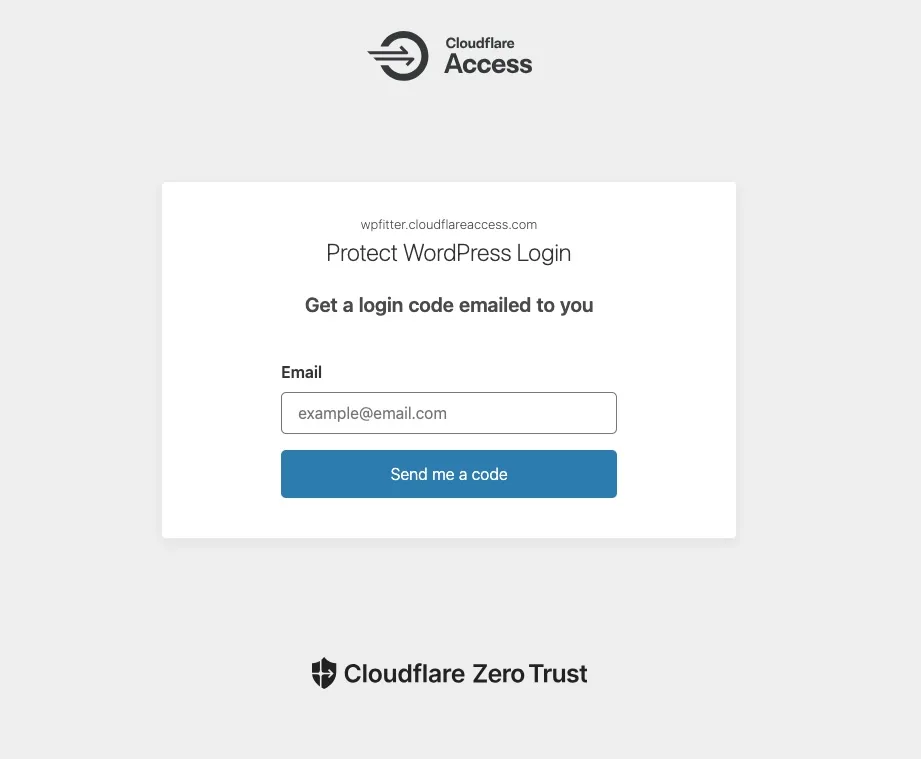
4. Choose Login Methods
Cloudflare Zero Trust supports:
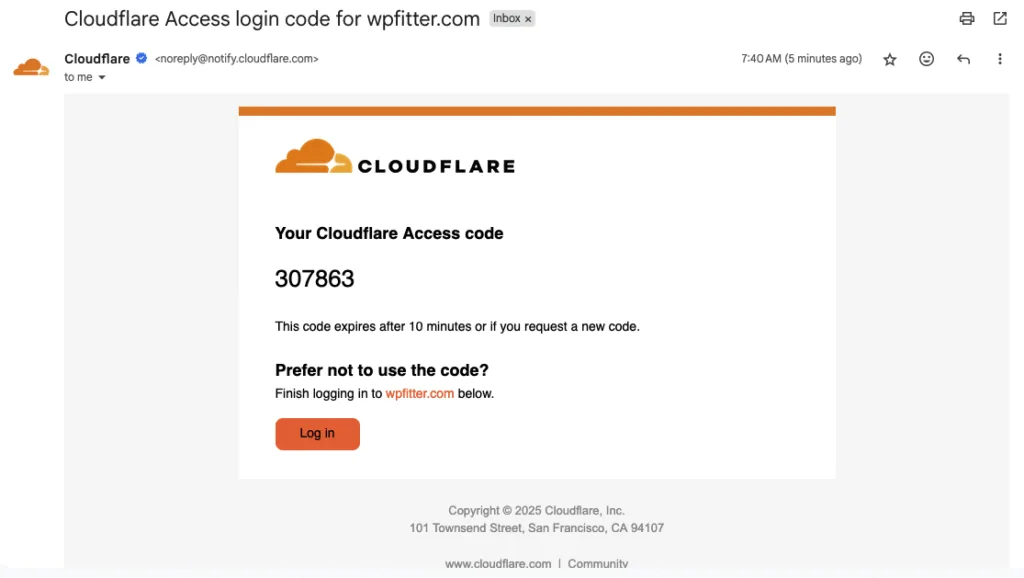
- One-Time Pin (OTP) via email.
- Identity providers (Google, Azure AD, etc.).
- Multi-factor authentication (MFA) for added security.
Set up these options under the authentication settings, as preferred for your users.
Note: Free users cannot modify this section – One-Time Pin is enabled by default.
5. Deploy and Test
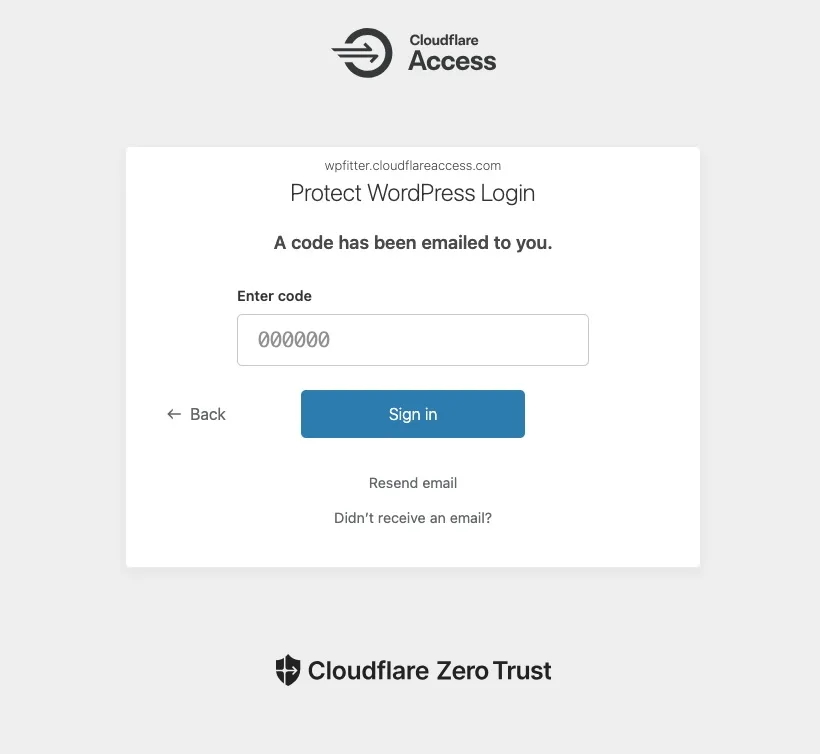
- Save and deploy the application.
- Open an incognito window or log out and visit
/wp-login.php; Cloudflare should intercept and require authentication. - Test using approved credentials to ensure access, and verify unauthorized access is blocked.
Conclusion
In essence, Cloudflare Zero Trust is a “front door” for your login page—if attackers don’t have the right keys (authenticated credentials), they simply cannot even attempt a password, stopping brute-force attacks cold.
If you maintain a WordPress site, this is one of the most reliable steps you can take to safeguard it for the long term.